I’m a software engineer and I love actual technology, but I think we have reached the peak of mt. stupid
Sick, so now I get to worry about the fucking emergency exits being ripped off the plane I’m flying on because the network connected torque wrench was hacked and displayed the proper torque setting while under torquing the bolts.
Can we not connect every fucking thing to the Internet?
I think we have reached the peak of mt. stupid
Not even close.
30 years ago I had a friendly discussion with an experienced veteran engineer, in which I pointed out the cranes moving tons of molten steel around the factory, were remote controlled with no encryption or security in sight. The response I got:
“LOL. We don’t need any of that, who would ever want to mess with (a crane carrying some tons of hot molten steel)?”
As IoT has slowly clawed its way into more and more places, we can see over and over the same “factory engineering” approach to security: “Who would ever want to mess with X?”. Well, turns out every hacker out there would want to mess with your webcam, smart tv, fridge, toaster, lights, fan, switch strip, vacuum, crane, drill, centrifuge, and everything with a processor in it… either to siphon data, for a botnet, as an entry point, for ransom, for sabotage, or just for the lulz!
As microcontrollers become cheaper, IPv6 expands to have them all publicly addressable, and people keep falling from the “controllable from your phone” into the “controllable from your AR viewer”…
Behold: Mt. ID-IoT looms ahead. 🏔️
I still don’t understand why a wrench needs to be connected to a network, even a wrench that makes very precise torque measurements.
In an ideal world: a wrench would self-adjust torque limits for every particular bolt, get that data directly from the plans for the part being worked on, and log every wrenching operation for quality control and compliance purposes.
In the real world: because it’s another bullet point the manufacturer can charge for.
I’m guessing it’s about documenting the assembly of safety-critical components. If some part of, let’s say an airplane fails because a bolt comes loose, the manufacturer wants to have a paper trail attached to it to prove that this specific bolt was indeed torqued to the correct spec. Connecting the wrench to the network could make this documentation much easier.
Changes the torque and the application of said torque for each bolt. As in “tool head has 5° of give until in place, then in ramps torque to 5nM over half a second, and holds for 1 second and then ramps to zero over .1 seconds”, and then something different for the next bolt. Then it logs that it did this for each bolt.
The tool can also be used to measure and correct the bolts as part of an inspection phase, and log the results of that inspection.
Finally, it tracks usage of the tool and can log that it needs maintenance or isn’t working correctly even if it’s just a subtle failure.Management wants the data so they can blame workers.
deleted by creator
Silicon Valley is no longer a place or even a mindset, it’s a greasy snake oil salesman.
I’m afraid this particular mindset predates Silicon Valley.
this is the “can it run DOOM” of manufacturing
🤖 I’m a bot that provides automatic summaries for articles:
Click here to see the summary
Researchers have unearthed nearly two dozen vulnerabilities that could allow hackers to sabotage or disable a popular line of network-connected wrenches that factories around the world use to assemble sensitive instruments and devices.
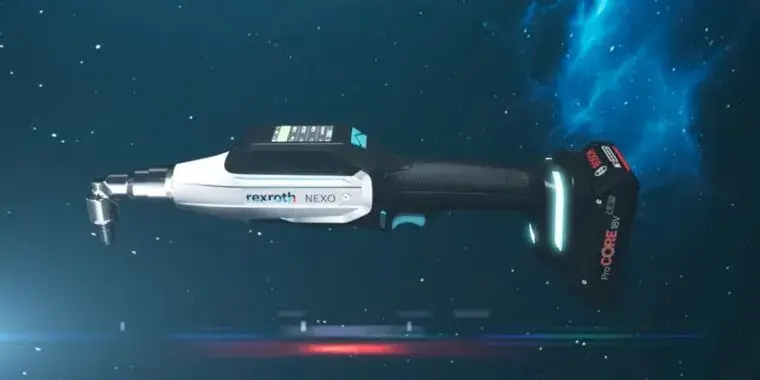
The vulnerabilities, reported Tuesday by researchers from security firm Nozomi, reside in the Bosch Rexroth Handheld Nutrunner NXA015S-36V-B.
The cordless device, which wirelessly connects to the local network of organizations that use it, allows engineers to tighten bolts and other mechanical fastenings to precise torque levels that are critical for safety and reliability.
The Nutrunner provides a torque-level indicator display that’s backed by a certification from the Association of German Engineers and adopted by the automotive industry in 1999.
The malware could then be used to disable entire fleets of the devices or to cause them to tighten fastenings too loosely or tightly while the display continues to indicate the critical settings are still properly in place.
The vulnerabilities found on the Bosch Rexroth NXA015S-36V-B allow an unauthenticated attacker who is able to send network packets to the target device to obtain remote execution of arbitrary code (RCE) with root privileges, completely compromising it.
Saved 46% of original text.